Imagine waking up tomorrow to find all your Bitcoins, bank passwords, and encrypted data deciphered in seconds. That's the "Q-Day" scenario — when quantum computers become powerful enough to break all modern encryption. And that day is closer than you think.
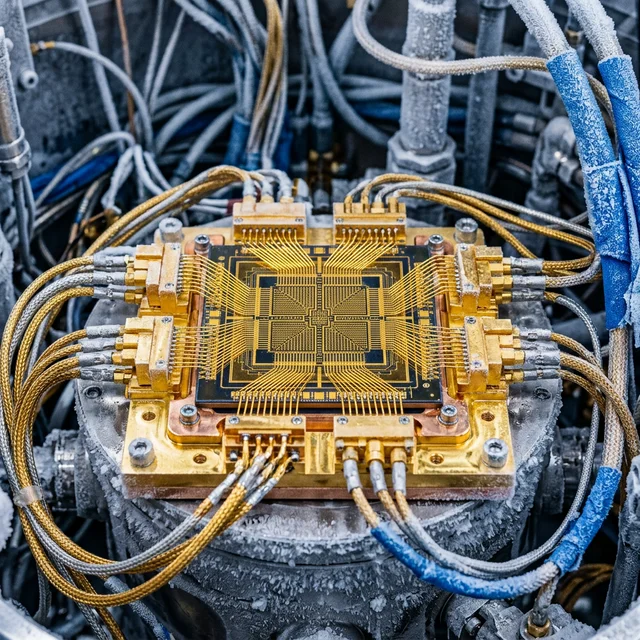
Classical vs Quantum Computer
| Aspect | Classical | Quantum |
|---|---|---|
| Basic unit | Bit (0 or 1) | Qubit (0, 1, or both simultaneously) |
| Processing | Sequential | Parallel (millions simultaneous) |
| Principle | Silicon transistors | Superposition + entanglement |
| Temperature | Room temp (~25°C) | Near absolute zero (-273°C) |
| Speed example | Benchmark: 10²⁵ years | Same: 5 minutes (Google Willow) |
Qubit Power Scale
- 1 qubit = 2 simultaneous states
- 100 qubits = more states than atoms in the universe
- 300 qubits = incomprehensible computational power
The Quantum Giants
Google Willow (Dec 2024)
105 qubits. Solved in 5 minutes what would take classicals 10²⁵ years. Demonstrated below-threshold error correction in Feb 2026.
IBM 2026 Roadmap
- Nighthawk: 360 qubits (3×120 modules), 7,500 gates
- Kookaburra: qLDPC memory + Logical Processing Unit
- Starling (2029): 200 logical qubits, 100M operations
| Company | Processor | Qubits | Approach |
|---|---|---|---|
| Willow | 105 | Superconducting | |
| IBM | Nighthawk | 360 | Superconducting |
| Microsoft | Majorana 1 | 8 | Topological |
| China | Jiuzhang 3 | 255 | Photonic |
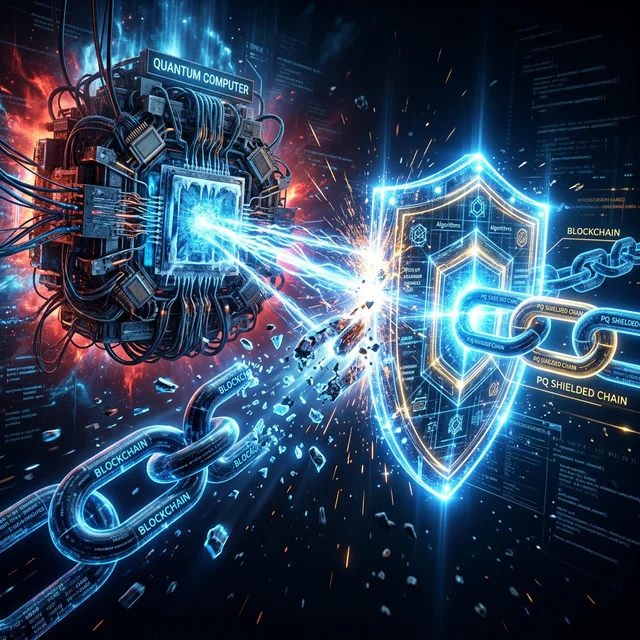
How Quantum Threatens Blockchain
| Algorithm | Used In | Quantum Vulnerability |
|---|---|---|
| ECC | Bitcoin/Ethereum signatures | ☠️ FATAL — Shor's algorithm |
| RSA | Web authentication, SSL/TLS | ☠️ FATAL — Shor's algorithm |
| SHA-256 | Bitcoin hashing | ⚠️ WEAKENED — Grover halves security |
"Harvest Now, Decrypt Later"
Governments are collecting encrypted data NOW to decrypt when quantum computers are ready.
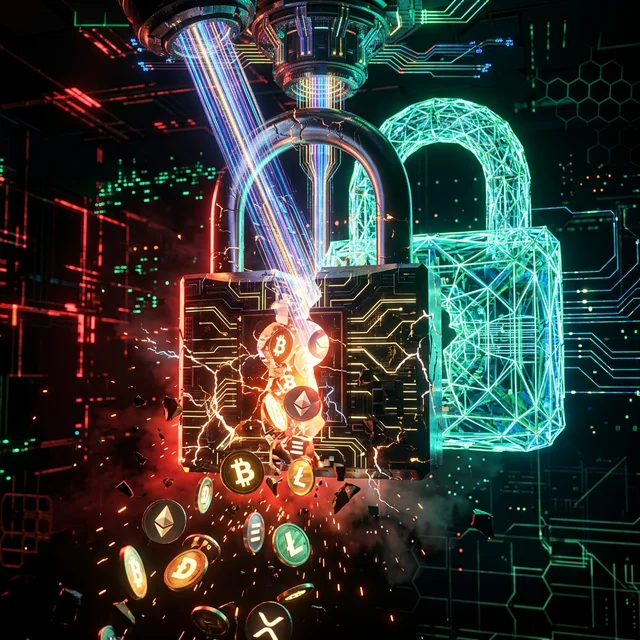
Bitcoin at Risk
25-30% of Bitcoin supply (4.5M BTC, ~$400B) sits in addresses with exposed public keys — including Satoshi's 1M BTC.
Post-Quantum Cryptography Defenses
| Algorithm | Type | Purpose |
|---|---|---|
| CRYSTALS-Dilithium | Lattice-based | Digital signatures |
| Falcon | Lattice-based | Compact signatures |
| SPHINCS+ | Hash-based | Signatures (no lattices) |
| CRYSTALS-Kyber | Lattice-based | Key encapsulation |
| Project | 2026 Action |
|---|---|
| Bitcoin (BIP 360) | Quantum-resistant address format |
| Ethereum | Hash-based validator signatures |
| QRL | 100% quantum-safe from inception |
When Is Q-Day?
| Prediction | Source | When |
|---|---|---|
| Optimistic | IBM, Google | 2035-2040 |
| Intermediate | Security experts | 2030-2035 |
| Pessimistic | Intelligence agencies | 2027-2030 |
Real-World Quantum Applications in 2026
Banking and Finance
The financial sector is among the most vulnerable — and most proactive — in preparing for quantum threats:
| Institution | Action | Timeline |
|---|---|---|
| JPMorgan Chase | Testing PQC across internal systems | 2025-2027 |
| HSBC | First bank to complete quantum-safe trading test | Q4 2025 |
| Bank of America | $200M investment in quantum readiness | 2024-2028 |
| Central Bank of Brazil | PQC pilot for PIX system | 2026 |
| ECB | Quantum risk assessment for SEPA | 2025-2026 |
Drug Discovery
Quantum computers can simulate molecular interactions that classical computers cannot, accelerating drug discovery:
- Protein folding: Quantum simulations reduce analysis from months to hours
- Drug interactions: Predicting side effects before clinical trials
- Personalized medicine: Modeling individual genetic responses to treatments
- Cost reduction: Estimated $100B savings in pharmaceutical R and D by 2035
The "Harvest Now, Decrypt Later" Threat
Perhaps the most unsettling scenario is already underway. Intelligence agencies and criminal organizations are collecting encrypted data today with the plan to decrypt it when quantum computers become powerful enough. This means:
- Diplomatic communications sent in 2024 could be readable by 2032
- Medical records encrypted today may be exposed in the next decade
- Financial transactions are being stored for future exploitation
- Military communications could be compromised retroactively
NIST officially standardized three post-quantum cryptographic algorithms in August 2024: CRYSTALS-Kyber (key encapsulation), CRYSTALS-Dilithium (digital signatures), and SPHINCS+ (hash-based signatures). Organizations that begin migration now will have a 5-10 year head start.
The Global Quantum Race
Who Is Leading?
| Country | Investment 2024-2026 | Qubits Record | Key Players |
|---|---|---|---|
| China | $15B+ | 1,000+ (photonic) | Baidu, Origin Quantum |
| USA | $5B (CHIPS Act quantum) | 1,121 (IBM Condor) | IBM, Google, Microsoft |
| EU | €7.2B (Quantum Flagship) | 127 (IQM) | IQM, Pasqal |
| Canada | $1.7B | 5,000+ (D-Wave annealing) | D-Wave, Xanadu |
| Japan | $1.5B | 64 (Fujitsu) | Fujitsu, NTT |
Different Approaches
Not all quantum computers are the same. The main competing technologies are:
- Superconducting (IBM, Google) — Requires near absolute zero temperatures. Most mature technology
- Trapped Ions (IonQ, Quantinuum) — More stable qubits but slower gate speeds
- Photonic (Xanadu, PsiQuantum) — Room temperature operation but harder to scale
- Topological (Microsoft) — Most stable in theory but still in research phase
- Neutral Atoms (Pasqal, QuEra) — Promising for large-scale quantum simulation
The race is not just about qubit count — error correction is the real bottleneck. Current quantum computers make errors at rates of 1 in 1,000 operations, while useful computation requires error rates below 1 in a billion.
Impact on Blockchain
Bitcoin and most cryptocurrencies use ECDSA (Elliptic Curve Digital Signature Algorithm), which is vulnerable to quantum attacks:
- Timeline: Estimates range from 2030-2040 for breaking Bitcoin keys
- Mitigation: Several quantum-resistant blockchain projects are in development (QRL, IOTA)
- Bitcoin response: The community is debating when to hard-fork to PQC signatures
- Ethereum: Vitalik Buterin has outlined a quantum-safe migration roadmap
Preparing Your Organization for Q-Day
Migration Roadmap
Security experts recommend a phased approach to post-quantum readiness:
- Inventory (2025-2026) — Catalog all cryptographic assets: TLS certificates, VPN configurations, code signing, SSH keys, database encryption
- Risk Assessment (2026) — Identify data with long-term confidentiality needs (medical, financial, government)
- Hybrid Deployment (2026-2028) — Run classical and PQC algorithms in parallel
- Testing (2027-2029) — Performance benchmarks, compatibility checks, interoperability
- Full Migration (2028-2032) — Replace all vulnerable cryptography with PQC standards
The Cost of Waiting
Organizations that delay PQC migration face exponentially increasing costs and risk. The average enterprise has over 250,000 cryptographic keys to manage. Each year of delay adds approximately 15-20 percent to total migration cost due to technical debt and increased attack surface. Those who act now will be positioned to lead in the quantum-safe era.
Conclusion
The question isn't IF encryption will be broken. The question is WHEN — and whether you'll be ready.
The future is already being calculated. In superposition.





